C. Scott Brown / Android Authority
TL;DR
- Google has announced that they are winding down the Google Play Security Reward Program.
- The program was introduced in late 2017 to incentivize security researchers to find and responsibly disclose vulnerabilities in popular Android apps.
- Google says they’re winding down the program due to a decrease in actionable vulnerabilities reported by security researchers.
Security vulnerabilities are lurking in most of the apps you use on a day-to-day basis; there’s just no way for most companies to preemptively fix every possible security issue because of human error, deadlines, lack of resources, and a multitude of other factors. That’s why many organizations run bug bounty programs to get external help with fixing these issues. The Google Play Security Reward Program (GPSRP) is an example of a bug bounty program that paid security researchers to find vulnerabilities in popular Android apps, but it’s being shut down later this month.
Google announced the Google Play Security Reward Program back in October 2017 as a way to incentivize security searchers to find and, most importantly, responsibly disclose vulnerabilities in popular Android apps distributed through the Google Play Store.
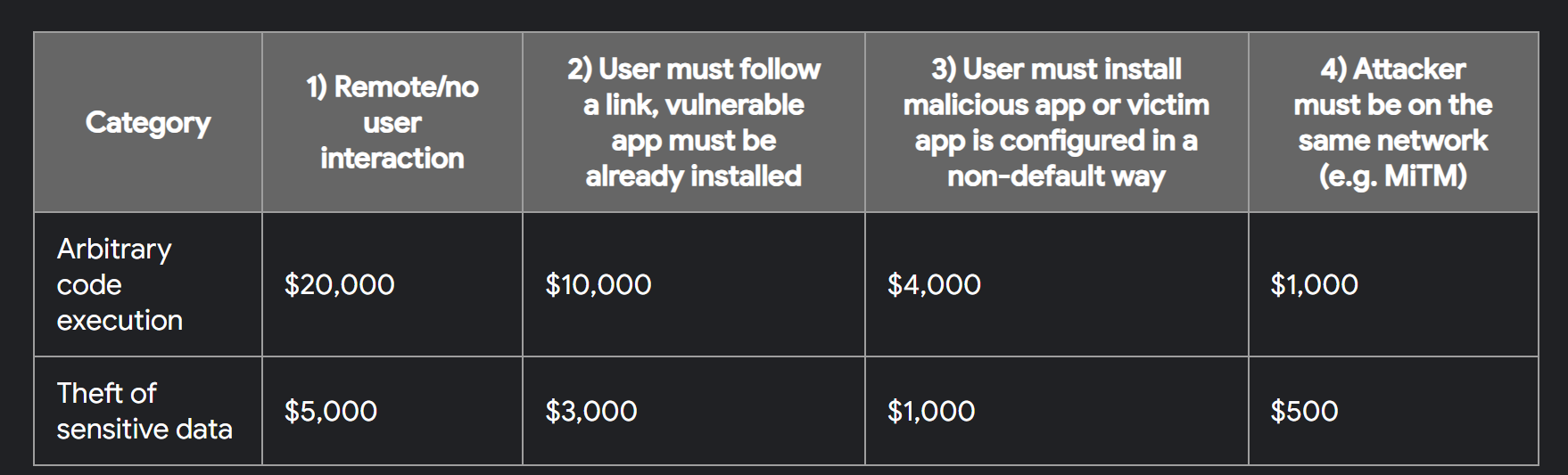
When the GPSRP first launched, it was limited to a select number of developers who were only allowed to submit eligible vulnerabilities that affected applications from a small number of participating developers. Eligible vulnerabilities include those that lead to remote code execution or theft of insecure private data, with payouts initially reaching a maximum of $5,000 for vulnerabilities of the former type and $1,000 for the latter type.
Over the years, the scope of the Google Play Security Reward Program program expanded to cover developers of some of the biggest Android apps such as Airbnb, Alibaba, Amazon, Dropbox, Facebook, Grammarly, Instacart, Line, Lyft, Opera, Paypal, Pinterest, Shopify, Snapchat, Spotify, Telegram, Tesla, TikTok, Tinder, VLC, and Zomato, among many others.
In August 2019, Google opened up the GPSRP to cover all apps in Google Play with at least 100 million installations, even if they didn’t have their own vulnerability disclosure or bug bounty program. In July 2019, the rewards were increased to a maximum of $20,000 for remote code execution bugs and $3,000 for bugs that led to the theft of insecure private data or access to protected app components.
Mishaal Rahman / Android Authority
The purpose of the Google Play Security Reward Program was simple: Google wanted to make the Play Store a more secure destination for Android apps. According to the company, vulnerability data they collected from the program was used to help create automated checks that scanned all apps available in Google Play for similar vulnerabilities. In 2019, Google said these automated checks helped more than 300,000 developers fix more than 1,000,000 apps on Google Play. Thus, the downstream effect of the GPSRP is that fewer vulnerable apps are distributed to Android users.
However, Google has now decided to wind down the Google Play Security Reward Program. In an email to participating developers, such as Sean Pesce, the company announced that the GPSRP will end on August 31st.
The reason they gave is that the program has seen a decrease in the number of actionable vulnerabilities reported. Google credits this success to the “overall increase in the Android OS security posture and feature hardening efforts.”
The full email sent to developers is reproduced below:
“Dear Researchers,
I hope this email finds you well. I am writing to express my sincere gratitude to all of you who have submitted bugs to the Google Play Security Reward Program over the past few years. Your contributions have been invaluable in helping us to improve the security of Android and Google Play.
As a result of the overall increase in the Android OS security posture and feature hardening efforts, we’ve seen fewer actionable vulnerabilities reported by the research community. Due to this decrease in actionable vulnerabilities reported, we are winding down the GPSRP program. The GPSRP program will end on August 31st. Any reports submitted before then will be triaged by September 15th. Final reward decisions will be made before September 30th when the program is officially discontinued. Final payments may take a few weeks to process.
I want to assure you that all of your reports will be reviewed and addressed before the program ends. We greatly value your input and want to make sure that any issues you have identified are resolved.
Thank you again for your support of the GPSRP program. We hope that you will continue working with us, on programs like the Android and Google Devices Security Reward Program.
Best regards,
Tony
On behalf of the Android Security Team”
In September of 2018, nearly a year after the GPSRP was announced, Google said that researchers had reported over 30 vulnerabilities through the program, earning a combined bounty of over $100k. Approximately a year later, in August of 2019, Google said that the program had paid out over $265k in bounties.
As far as we know, the company hasn’t disclosed how much they’ve paid out to security researchers since then, but we’d be surprised if the number isn’t notably higher than $265k given how long it’s been since the last disclosure and the number of popular apps in the crosshairs of security researchers.
Google shutting down this program is a mixed bag for users. On one hand, it means that popular apps have largely gotten their act together, but on the other hand, it means that some security researchers won’t have the incentive to disclose any future vulnerabilities responsibly, especially if those vulnerabilities impact an app made by a developer who doesn’t run their own bug bounty program.

