Google has released a new emergency Chrome security update to address the third zero-day vulnerability exploited in attacks within a week.
“Google is aware that an exploit for CVE-2024-4947 exists in the wild,” the search giant said in a security advisory published on Wednesday.
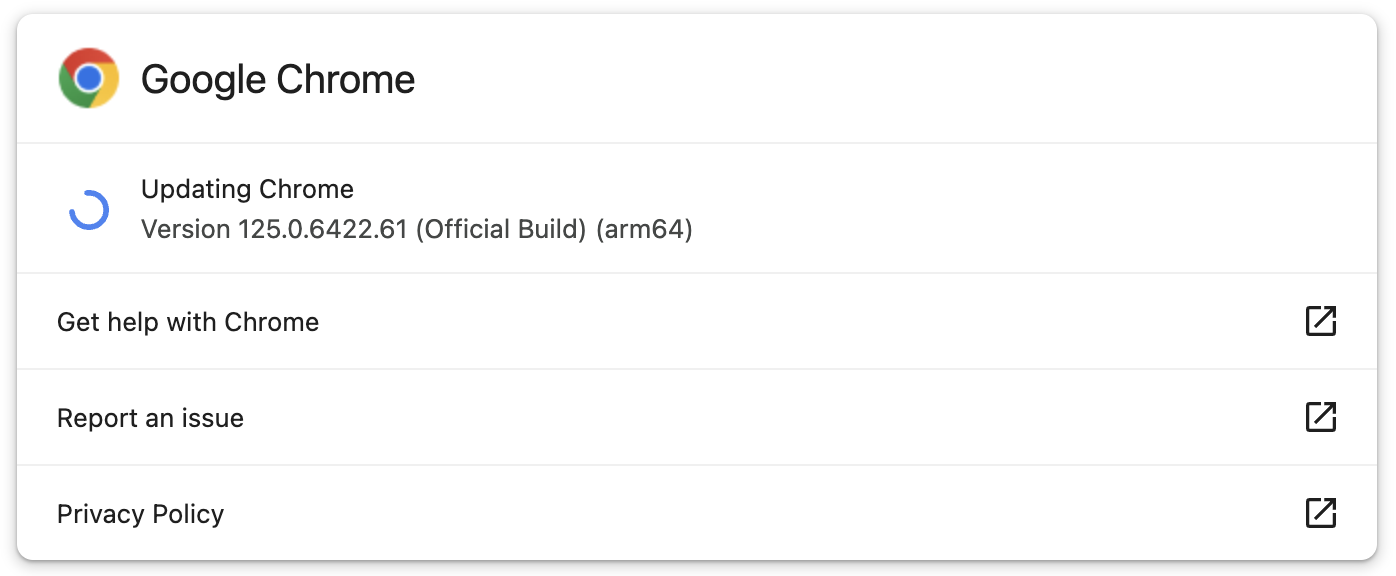
The company fixed the zero-day flaw with the release of 125.0.6422.60/.61 for Mac/Windows and 125.0.6422.60 (Linux). The new versions will roll out to all users in the Stable Desktop channel over the coming weeks.
Chrome updates automatically when security patches are available. However, users can also confirm they’re running the latest version by going to Chrome menu > Help > About Google Chrome, letting the update finish, and then clicking on the ‘Relaunch’ button to install it.
Today’s update was immediately available when BleepingComputer checked for new updates.
The high-severity zero-day vulnerability (CVE-2024-4947) is caused by a type confusion weakness in the Chrome V8 JavaScript engine reported by Kaspersky’s Vasily Berdnikov and Boris Larin.
Even though such vulnerabilities generally enable threat actors to trigger browser crashes by reading or writing memory out of buffer bounds, they can also exploit them for arbitrary code execution on targeted devices.
While Google confirmed the CVE-2024-4947 bug was used in attacks, the company has yet to share more details regarding these incidents.
“Access to bug details and links may be kept restricted until a majority of users are updated with a fix,” Google said.
“We will also retain restrictions if the bug exists in a third party library that other projects similarly depend on, but haven’t yet fixed.”
Seventh actively exploited zero-day patched in 2024
This latest Chrome vulnerability is the seventh zero-day fixed in the Google web browser since the start of the year, with the complete list of zero-days patched in 2024 including:
- CVE-2024-0519: A high-severity out-of-bounds memory access weakness within the Chrome V8 JavaScript engine, allowing remote attackers to exploit heap corruption via a specially crafted HTML page, leading to unauthorized access to sensitive information.
- CVE-2024-2887: A high-severity type confusion flaw in the WebAssembly (Wasm) standard. It could lead to remote code execution (RCE) exploits leveraging a crafted HTML page.
- CVE-2024-2886: A use-after-free vulnerability in the WebCodecs API used by web applications to encode and decode audio and video. Remote attackers exploited it to perform arbitrary reads and writes via crafted HTML pages, leading to remote code execution.
- CVE-2024-3159: A high-severity vulnerability caused by an out-of-bounds read in the Chrome V8 JavaScript engine. Remote attackers exploited this flaw using specially crafted HTML pages to access data beyond the allocated memory buffer, resulting in heap corruption that could be leveraged to extract sensitive information.
- CVE-2024-4671: A high-severity use-after-free flaw in the Visuals component that handles the rendering and displaying content in the browser.
- CVE-2024-4761: An out-of-bounds write problem in Chrome’s V8 JavaScript engine, which is responsible for executing JS code in the application.

