A new malware campaign is spreading a previously undocumented backdoor named “Voldemort” to organizations worldwide, impersonating tax agencies from the U.S., Europe, and Asia.
As per a Proofpoint report, the campaign started on August 5, 2024, and has disseminated over 20,000 emails to over 70 targeted organizations, reaching 6,000 in a single day at the peak of its activity.
Over half of all targeted organizations are in the insurance, aerospace, transportation, and education sectors. The threat actor behind this campaign is unknown, but Proofpoint believes the most likely objective is to conduct cyber espionage.
The attack is similar to what Proofpoint described at the start of the month but involved a different malware set in the final stage.
Impersonating tax authorities
A new Proofpoint report says the attackers are crafting phishing emails to match a targeted organization’s location based on public information.
The phishing emails impersonate taxing authorities from the organization’s country, stating that there is updated tax information and includes links to associated documents.
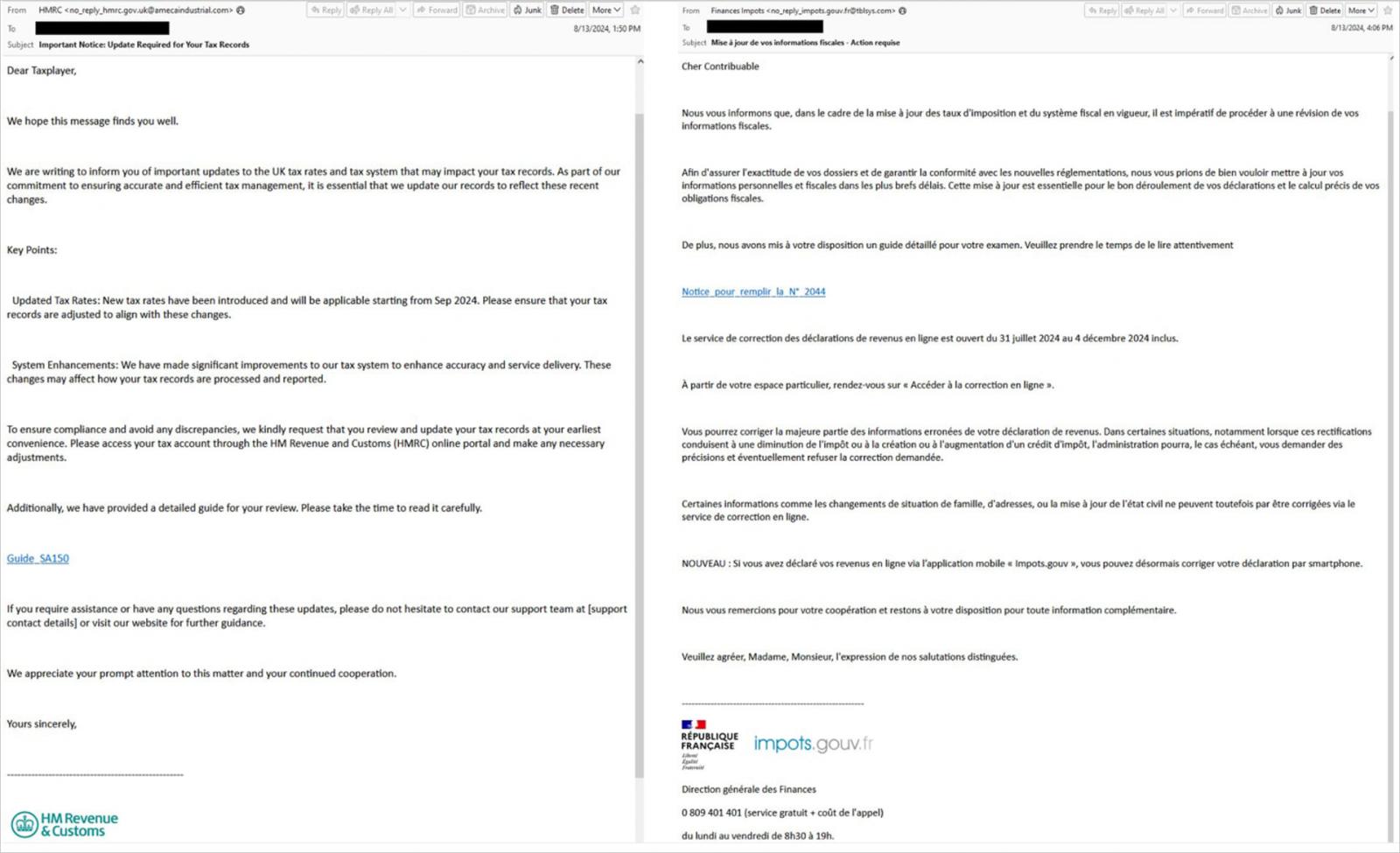
Source: Proofpoint
Clicking on the link brings recipients to a landing page hosted on InfinityFree, which uses Google AMP Cache URLs to redirect the victim to a page with a “Click to view document” button.
When the button is clicked, the page will check the browser’s User Agent, and if it’s for Windows, redirect the target to a search-ms URI (Windows Search Protocol) that points to a TryCloudflare-tunneled URI. Non-Windows users are redirected to an empty Google Drive URL that serves no malicious content.
If the victim interacts with the search-ms file, Windows Explorer is triggered to display a LNK or ZIP file disguised as a PDF.
The use of the search-ms: URI has become popular lately with phishing campaigns as even though this file is hosted on an external WebDAV/SMB share, it is made to appear as if it resides locally in the Downloads folder to trick the victim into opening it.
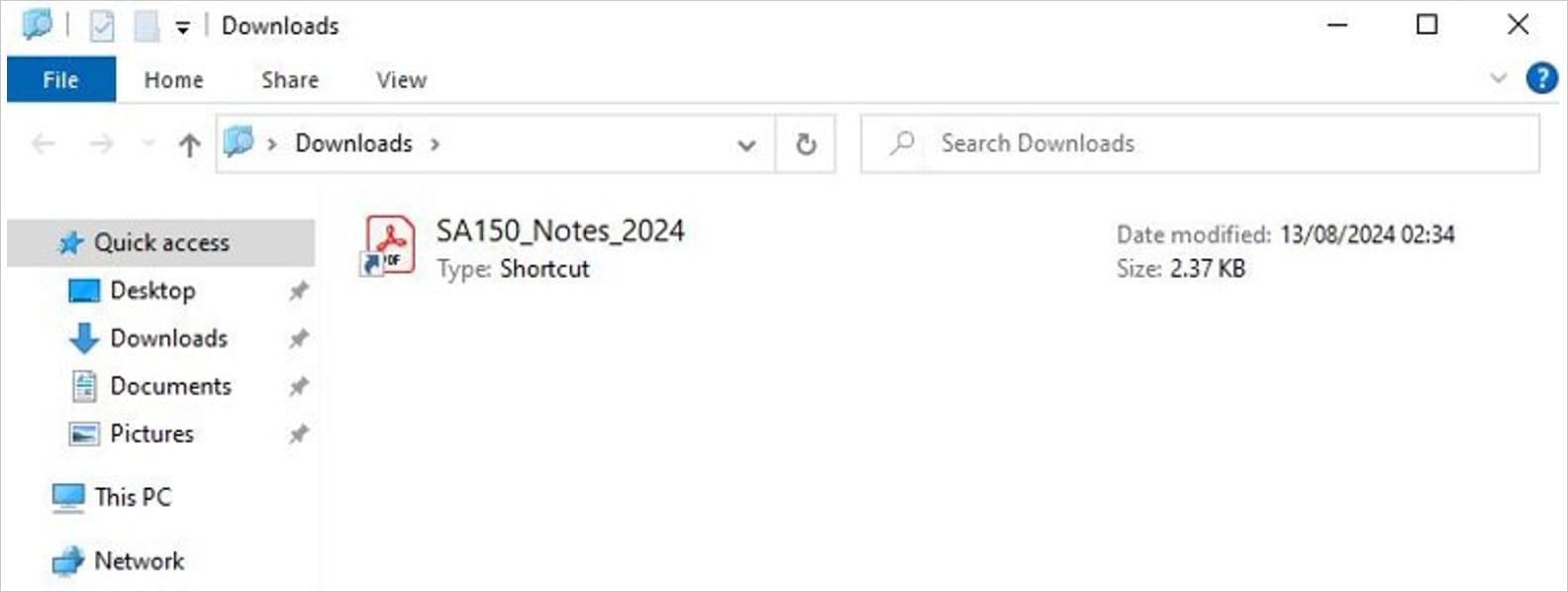
Source: Proofpoint
Doing so executes a Python script from another WebDAV share without downloading it on the host, which performs system info collection to profile the victim. At the same time, a decoy PDF is displayed to obscure the malicious activity.
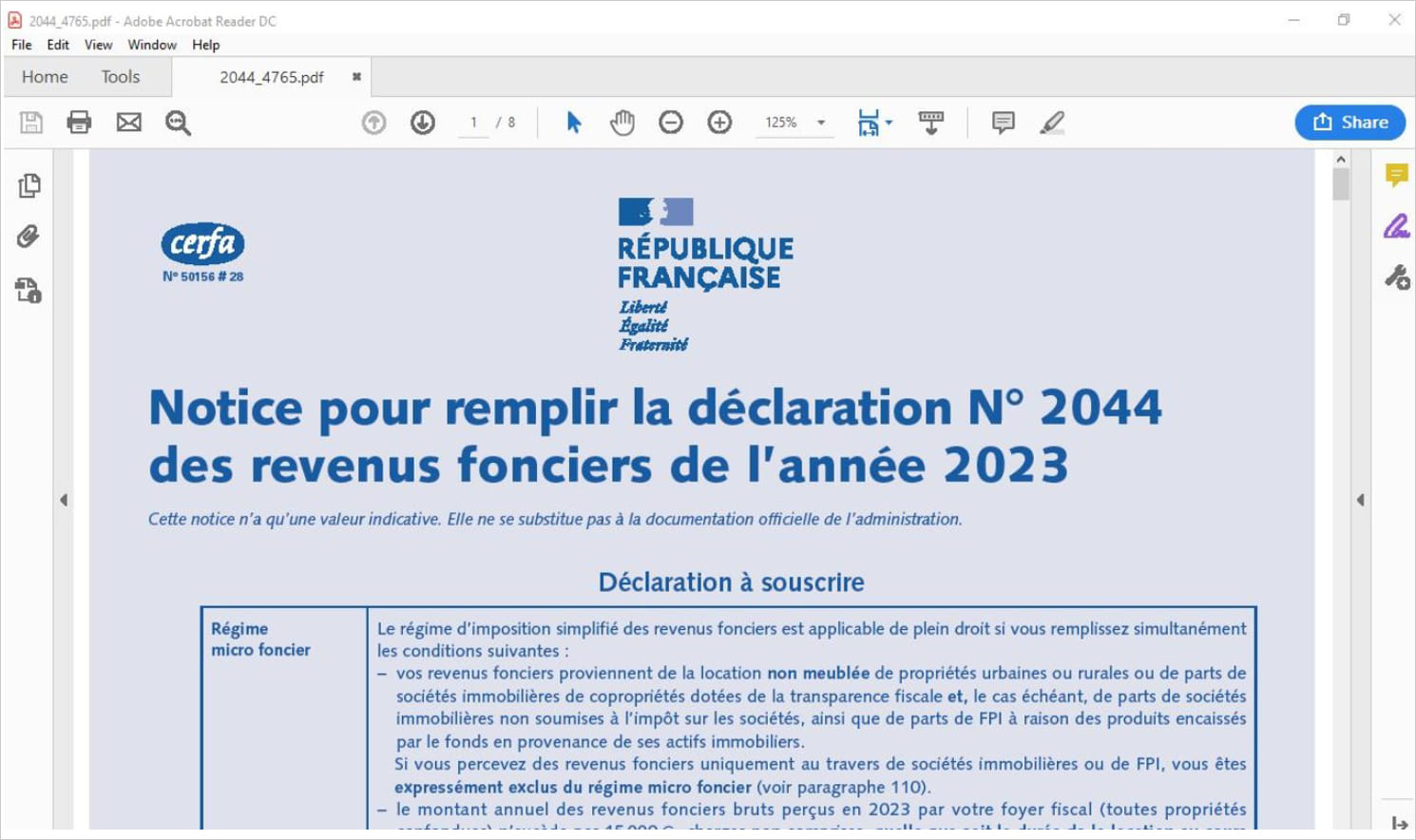
Source: Proofpoint
The script also downloads a legitimate Cisco WebEx executable (CiscoCollabHost.exe) and a malicious DLL (CiscoSparkLauncher.dll) to load Voldemort using DLL side-loading.
Abuse of Google Sheets
Voldemort is a C-based backdoor that supports a wide range of commands and file management actions, including exfiltration, introducing new payloads into the system, and file deletion.
The list of supported commands is given below:
- Ping – Tests the connectivity between the malware and the C2 server.
- Dir – Retrieves a directory listing from the infected system.
- Download – Downloads files from the infected system to the C2 server.
- Upload – Uploads files from the C2 server to the infected system.
- Exec – Executes a specified command or program on the infected system.
- Copy – Copies files or directories within the infected system.
- Move – Moves files or directories within the infected system.
- Sleep – Puts the malware into sleep mode for a specified duration, during which it will not perform any activities.
- Exit – Terminates the malware’s operation on the infected system.
A notable feature of Voldemort is that it uses Google Sheets as a command and control server (C2), pinging it to get new commands to execute on the infected device and as a repository for stolen data.
Each infected machine writes its data to specific cells within the Google Sheet, which can be designated by unique identifiers like UUIDs, ensuring isolation and clearer management of the breached systems.
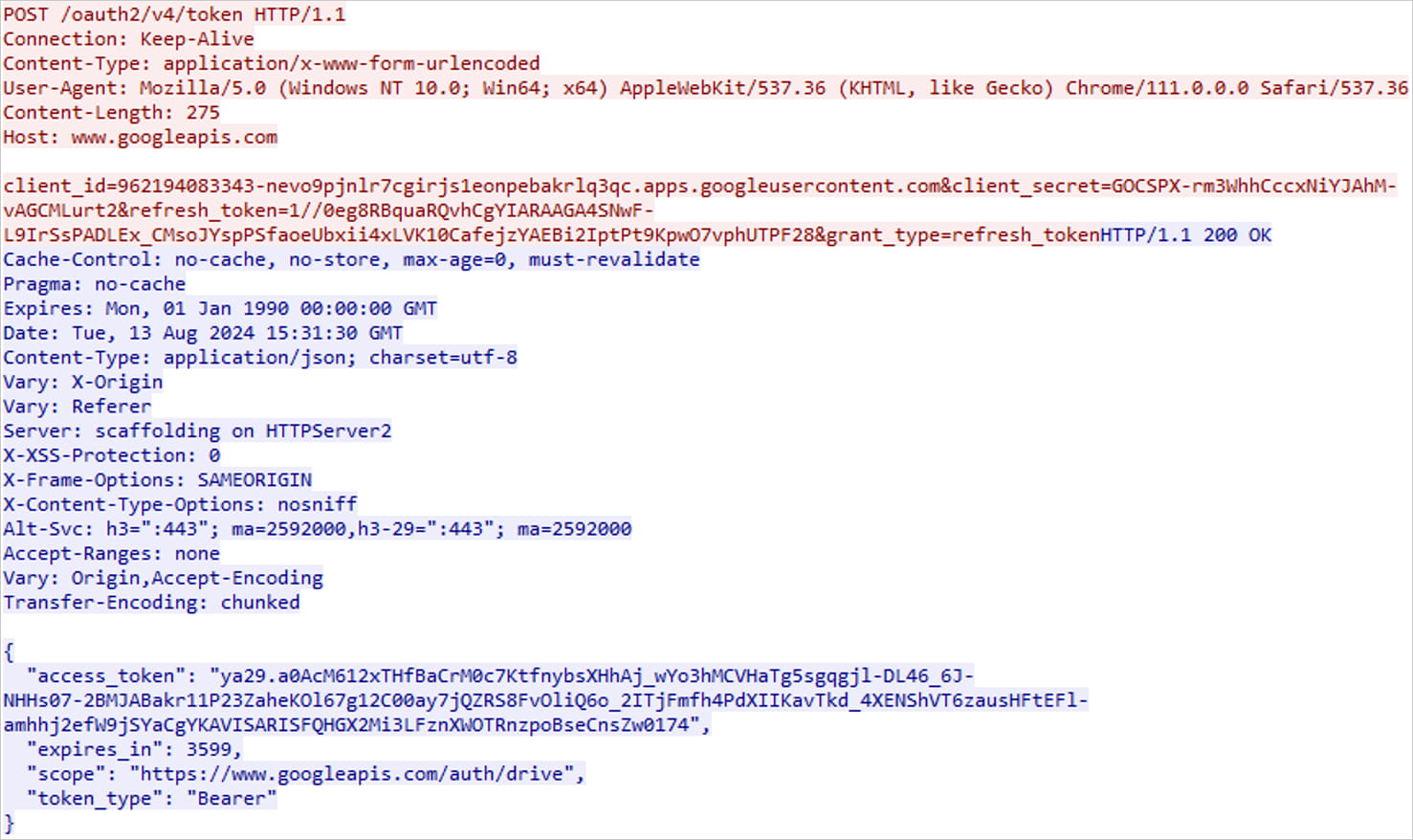
Source: Proofpoint
Voldemort uses Google’s API with an embedded client ID, secret, and refresh token to interact with Google Sheets, which are stored in its encrypted configuration.
This approach provides the malware with a reliable and highly available C2 channel, and also reduces the likelihood of network communication being flagged by security tools. As Google Sheets is commonly used in the enterprise, it also makes blocking the service impractical.
In 2023, the Chinese APT41 hacking group was previously seen using Google Sheets as a command and control server through the use of the red-teaming GC2 toolkit.
To defend against this campaign, Proofpoint recommends limiting access to external file-sharing services to trusted servers, blocking connections to TryCloudflare if not actively needed, and monitoring for suspicious PowerShell execution.

